Tag
#git
Cross Site Scripting vulnerability in tiagorlampert CHAOS v.5.0.1 allows a remote attacker to escalate privileges via the sendCommandHandler function in the handler.go component.
An issue in OpenStack magnum yoga-eom version allows a remote attacker to execute arbitrary code via the cert_manager.py. component.
### Summary Timber is vulnerable to [PHAR deserialization](https://portswigger.net/web-security/deserialization/exploiting#phar-deserialization) due to a lack of checking the input before passing it into the` file_exists()` function. If an attacker can upload files of any type to the server, he can pass in the `phar://` protocol to unserialize the uploaded file and instantiate arbitrary PHP objects. This can lead to remote code execution especially when Timber is used with frameworks with documented POP chains like Wordpress/ vulnerable developer code. ### Details The vulnerability lies in the run function within the `toJpg.php` file. The two parameters passed into it are not checked or sanitized, hence an attacker could potentially inject malicious input leading to Deserialization of Untrusted Data, allowing for remote code execution: 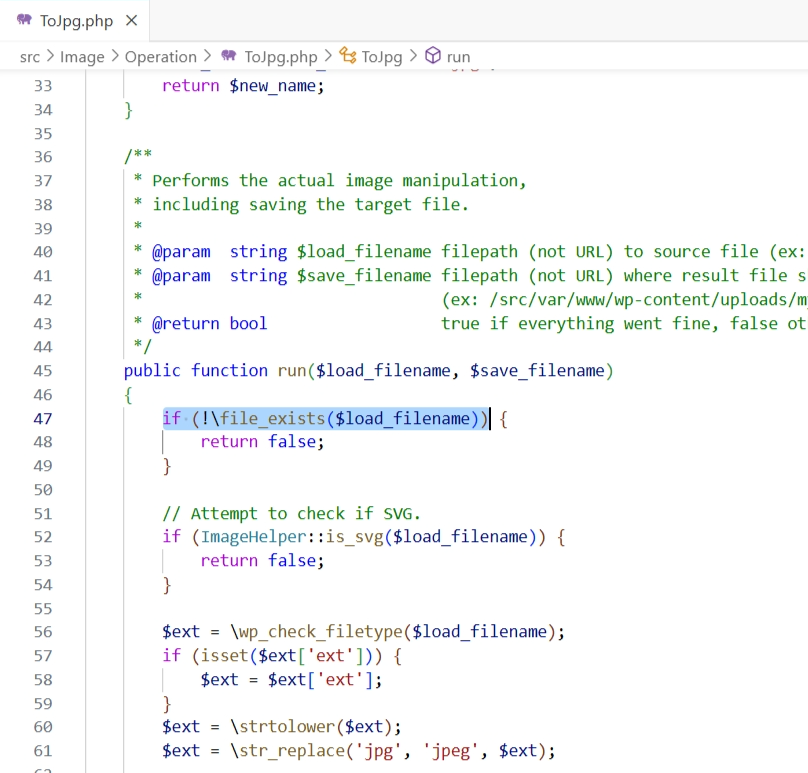 ### PoC Setup the following code in `/var/www/html`: `...
The Ray Project dashboard contains a CPU profiling page, and the format parameter is not validated before being inserted into a system command executed in a shell, allowing for arbitrary command execution. If the system is configured to allow passwordless sudo (a setup some Ray configurations require) this will result in a root shell being returned to the user. If not configured, a user level shell will be returned. Versions 2.6.3 and below are affected.
MinIO versions prior to 2024-01-31T20-20-33Z suffer from a privilege escalation vulnerability.
### Impact Prior to the patched version, logged in users of Mautic are vulnerable to a self XSS vulnerability in the notifications within Mautic. Users could inject malicious code into the notification when saving Dashboards. ### Patches Update to Mautic 4.4.12. ### Workarounds None ### References - https://owasp.org/www-project-top-ten/2017/A7_2017-Cross-Site_Scripting_(XSS) If you have any questions or comments about this advisory: Email us at [security@mautic.org](mailto:security@mautic.org)
An issue in tiagorlampert CHAOS v5.0.1 allows a remote attacker to execute arbitrary code via the BuildClient function within client_service.go
An issue discovered in Reportico Till 8.1.0 allows attackers to obtain sensitive information via execute_mode parameter of the URL.
By Waqas In this article, we will explore 12 paid and free OSINT tools that are publicly available and can be very useful when utilized properly and for appropriate purposes. This is a post from HackRead.com Read the original post: Best Paid and Free OSINT Tools for 2024
### Impact Prior to the patched version, there is an XSS vulnerability in the description fields within the Mautic application which could be exploited by a logged in user of Mautic with the appropriate permissions. This could lead to the user having elevated access to the system. ### Patches Update to 4.4.12 ### Workarounds None ### References - https://owasp.org/www-project-top-ten/2017/A7_2017-Cross-Site_Scripting_(XSS) - https://owasp.org/www-project-web-security-testing-guide/latest/4-Web_Application_Security_Testing/07-Input_Validation_Testing/02-Testing_for_Stored_Cross_Site_Scripting If you have any questions or comments about this advisory: Email us at [security@mautic.org](mailto:security@mautic.org)