Tag
#git
### Summary Security misconfiguration in edit configuration file API in dashboard component of ESPHome version 2023.12.9 (command line installation) allows authenticated remote attackers to read and write arbitrary files under the configuration directory rendering remote code execution possible. ### Details It is possible to abuse this path traversal vulnerability both in command line installation and Home Assistant add-on, but it is possible to read and write files only under the configuration directory. The vulnerability is present and exploitable in the command line installation, but it was not possible to confirm an impact in the home assistant add-on version. ### PoC <img width="482" alt="/edit?configuration=/config/.esphome/esphome.json" src="https://github.com/esphome/esphome/assets/115887876/d2da3180-976e-4bed-b4b9-35ac960a7fb4"> <br/> <img width="344" alt="/edit?configuration=/config/.esphome/build/test01/src/main.cpp (firmware for board named test01)" src="https://github...
### Impact Previously, budibase used a library called `vm2` for code execution inside the Budibase builder and apps, such as the UI below for configuring bindings in the design section. 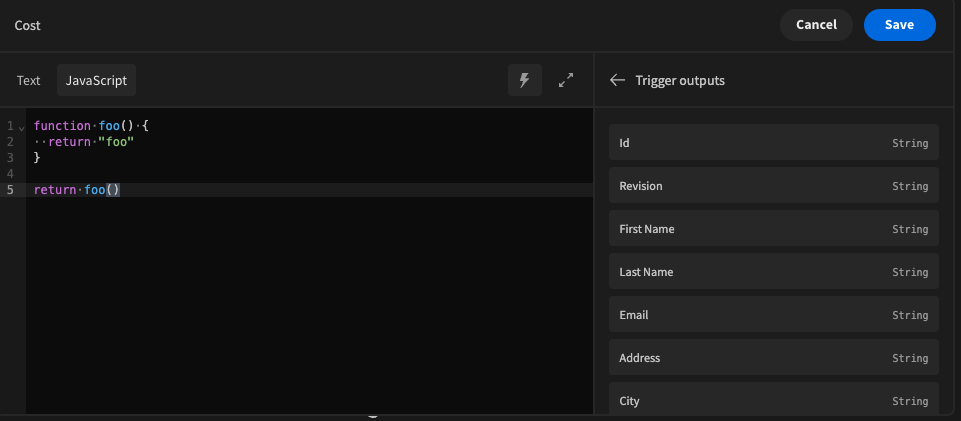 Due to a [vulnerability in vm2](https://github.com/advisories/GHSA-cchq-frgv-rjh5), any environment that executed the code server side (automations and column formulas) was susceptible to this vulnerability, allowing users to escape the sandbox provided by `vm2`, and to expose server side variables such as `process.env`. It's recommended by the authors of `vm2` themselves that you should move to another solution for remote JS execution due to this vulnerability. ### Patches We moved our entire JS sandbox infrastructure over to `isolated-vm`, a much more secure and recommended library for remote code execution in 2.20.0. This also comes with a performance benefit in the way w...
### Impact This vulnerability allows SQL injection when Parse Server is configured to use the PostgreSQL database. ### Patches The algorithm to detect SQL injection has been improved. ### Workarounds None. ### References - https://github.com/parse-community/parse-server/security/advisories/GHSA-6927-3vr9-fxf2 - https://github.com/parse-community/parse-server/releases/tag/6.5.0 (fixed in Parse Server 6) - https://github.com/parse-community/parse-server/releases/tag/7.0.0-alpha.20 (fixed in Parse Server 7 alpha release) ### Credits - Mikhail Shcherbakov (https://twitter.com/yu5k3) working with Trend Micro Zero Day Initiative (finder) - Ehsan Persania (remediation developer) - Manuel Trezza (coordinator)
Bagisto is vulnerable to cross-site scripting (XSS) via png file upload vulnerability in product review option.
Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') vulnerability in Apache Archiva. This issue affects Apache Archiva: from 2.0.0. As this project is retired, we do not plan to release a version that fixes this issue. Users are recommended to find an alternative or restrict access to the instance to trusted users. Alternatively, you could configure a HTTP proxy in front of your Archiva instance to only forward requests that do not have malicious characters in the URL. NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
** UNSUPPORTED WHEN ASSIGNED ** Incorrect Authorization vulnerability in Apache Archiva. Apache Archiva has a setting to disable user registration, however this restriction can be bypassed. As Apache Archiva has been retired, we do not expect to release a version of Apache Archiva that fixes this issue. You are recommended to look into migrating to a different solution, or isolate your instance from any untrusted users. NOTE: This vulnerability only affects products that are no longer supported by the maintainer
** UNSUPPORTED WHEN ASSIGNED ** Incorrect Authorization vulnerability in Apache Archiva: a vulnerability in Apache Archiva allows an unauthenticated attacker to modify account data, potentially leading to account takeover. This issue affects Apache Archiva: from 2.0.0. As this project is retired, we do not plan to release a version that fixes this issue. Users are recommended to find an alternative or restrict access to the instance to trusted users. NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
By Uzair Amir Just as surfing the web is better with a stable internet connection, completing tasks like web scraping or… This is a post from HackRead.com Read the original post: Diving Into Stability: How Static Proxies Transform Online Experience
By Deeba Ahmed Lookout urges crypto users to be on the lookout of the new and tricky phishing campaign. This is a post from HackRead.com Read the original post: CryptoChameleon Phishing Scam Targets Crypto Users and FCC Employees
### Impact SDK versions between and including 5.16.0 and 5.19.0 allowed Sentry auth tokens to be set in the optional authToken configuration parameter, for debugging purposes. Doing so would result in the auth token being built into the application bundle, and therefore the auth token could be potentially exposed in case the application bundle is subsequently published. You may ignore this notification if you are not using `authToken` configuration parameter in your React Native SDK configuration or did not publish apps using this way of configuring the `authToken`. If you had set the `authToken` in the plugin config previously, and built and published an app with that config, you should [rotate your token](https://docs.sentry.io/product/accounts/auth-tokens/). ### Patches The behavior that allowed setting an `authToken` parameter was fixed in SDK version 5.19.1 where, if this parameter was set, you will see a warning and the `authToken` would be removed before bundling the applicat...