Tag
#sql
Orange Station version 1.0 suffers from a remote shell upload vulnerability.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday placed three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerabilities added are as follows - CVE-2023-48788 (CVSS score: 9.3) - Fortinet FortiClient EMS SQL Injection Vulnerability CVE-2021-44529 (CVSS score: 9.8) - Ivanti
### Summary A SQL injection vulnerability has been discovered in the `insertentry` & `saveentry` when modifying records due to improper escaping of the email address. This allows any authenticated user with the rights to add/edit FAQ news to exploit this vulnerability to exfiltrate data, take over accounts and in some cases, even achieve RCE. ### PoC 1 - SQL Injection at insertentry: 1. Browse to “/admin/?action=editentry”, edit record and save. Intercept the POST request to "/admin/?action=insertentry" and modify the email and notes parameters in the body to the payloads below: a. `email=test'/*@email.com` b. `notes=*/,1,1,1,1,null,1);select+pg_sleep(5)--` 2. Send the request and notice the `pg_sleep(5)` command is executed with a time delay of 5 seconds in the response. This verifies that the SQL injection vulnerability exists. 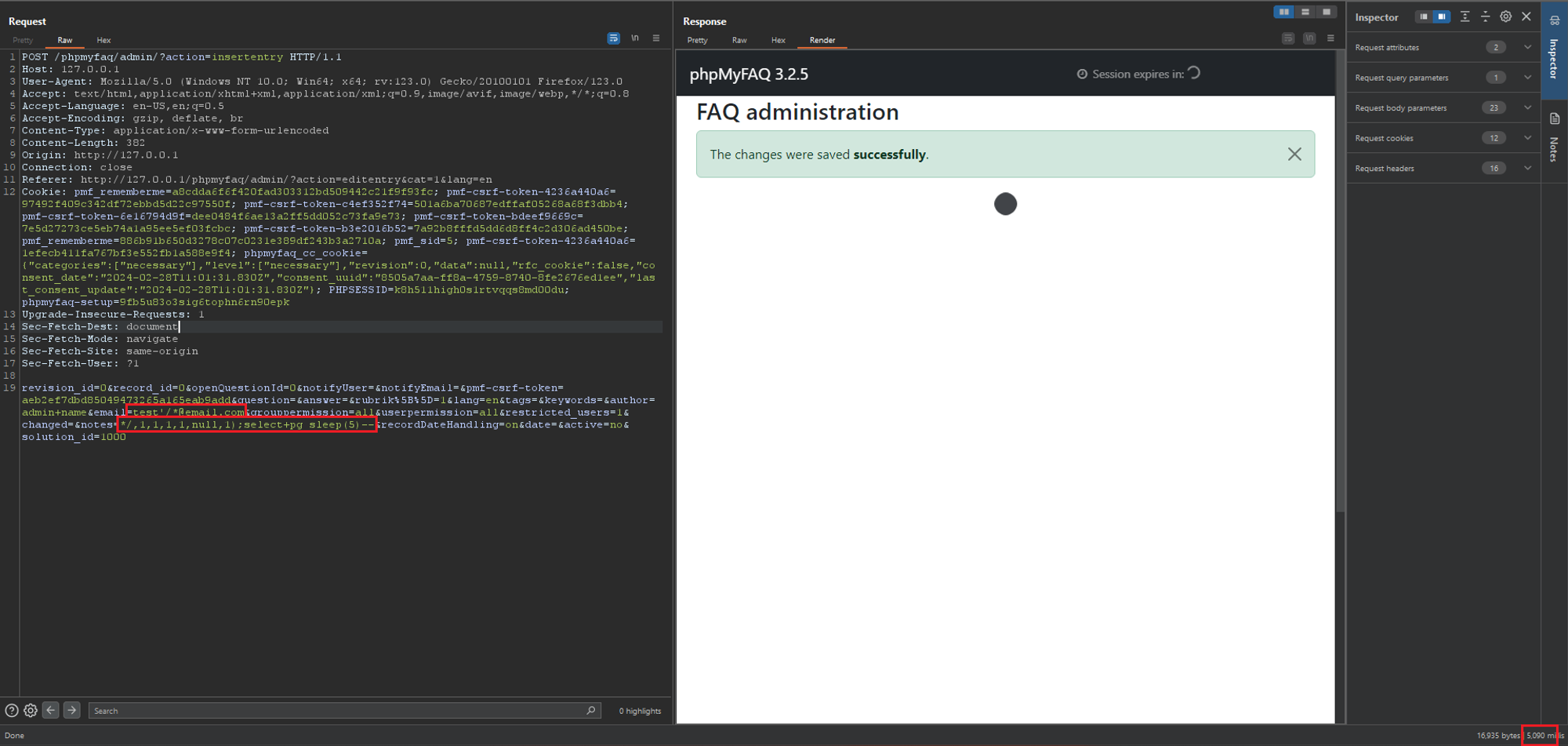 ### PoC 2 - SQL Injection at saveentry 1....
### Summary A SQL injection vulnerability has been discovered in the the "Add News" functionality due to improper escaping of the email address. This allows any authenticated user with the rights to add/edit FAQ news to exploit this vulnerability to exfiltrate data, take over accounts and in some cases, even achieve RCE. ### Details The vulnerable field lies in the `authorEmail` field which uses PHP's `FILTER_VALIDATE_EMAIL` filter. This filter is insufficient in protecting against SQL injection attacks and should still be properly escaped. However, in this version of phpMyFAQ (3.2.5), this field is not escaped properly can be used together with other fields to fully exploit the SQL injection vulnerability. ### PoCs 4 PoCs are demonstrated here to illustrate the potential impacts. #### PoC 1 - Postgres Time Based SQLi 1. Login as admin or any user with the rights to view and save news. 2. Navigate to "../phpmyfaq/admin/?action=news", click on "Add news", fill in some data, send and...
### Impact WP Crontrol includes a feature that allows administrative users to create events in the WP-Cron system that store and execute PHP code [subject to the restrictive security permissions documented here](https://wp-crontrol.com/docs/php-cron-events/). While there is _no known vulnerability in this feature on its own_, there exists potential for this feature to be vulnerable to RCE if it were specifically targeted via vulnerability chaining that exploited a separate SQLi (or similar) vulnerability. This is exploitable on a site if one of the below preconditions are met: * The site is vulnerable to a writeable SQLi vulnerability in any plugin, theme, or WordPress core * The site's database is compromised at the hosting level * The site is vulnerable to a method of updating arbitrary options in the `wp_options` table * The site is vulnerable to a method of triggering an arbitrary action, filter, or function with control of the parameters ### Patches As a hardening measure, WP...
Task Management System version 1.0 suffers from multiple remote SQL injection vulnerabilities.
By Deeba Ahmed Pwn2Own is back! This is a post from HackRead.com Read the original post: Pwn2Own 2024 Awards $700k as Hackers Pwn Tesla, Browsers, and More
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 7.1 ATTENTION: Exploitable remotely/low attack complexity/public exploits are available Vendor: Advantech Equipment: WebAccess/SCADA Vulnerability: SQL Injection 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an authenticated attacker to read or modify a remote database. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Advantech WebAccess/SCADA, a bowser-based SCADA software, are affected: WebAccess/SCADA: Version 9.1.5U 3.2 Vulnerability Overview 3.2.1 IMPROPER NEUTRALIZATION OF SPECIAL ELEMENTS USED IN AN SQL COMMAND ('SQL INJECTION') CWE-89: There is a SQL Injection vulnerability in Advantech's WebAccess/SCDA software that allows an authenticated attacker to remotely inject SQL code on the database. Successful exploitation of this vulnerability could allow an attacker to read or modify data on the remote database. CVE-2024-2453 has been assigned to this vulnerability. A CVSS v3.1 base score of 6...
A vulnerability was found in Folio Spring Module Core before 2.0.0. Affected by this issue is the function dropSchema of the file tenant/src/main/java/org/folio/spring/tenant/hibernate/HibernateSchemaService.java of the component Schema Name Handler. The manipulation leads to sql injection. Upgrading to version 2.0.0 is able to address this issue. The name of the patch is d374a5f77e6b58e36f0e0e4419be18b95edcd7ff. It is recommended to upgrade the affected component. The identifier of this vulnerability is VDB-257516.
Atlassian has released patches for more than two dozen security flaws, including a critical bug impacting Bamboo Data Center and Server that could be exploited without requiring user interaction. Tracked as CVE-2024-1597, the vulnerability carries a CVSS score of 10.0, indicating maximum severity. Described as an SQL injection flaw, it's rooted in a dependency called org.postgresql: