Tag
#web
The advancement of technology has also impacted sectors like gaming. Blockchain technology has surfaced as an asset that…
Info stealers are thriving on Mac, with one specific variant accounting for 70% of all info stealer detections at the end of 2024.
Xerox Versalink printers are vulnerable to pass-back attacks. Rapid7 discovers LDAP & SMB flaws (CVE-2024-12510 & CVE-2024-12511). Update…
A new report reveals how cheap Infostealer malware is exposing US military and defense data, putting national security at risk. Hackers exploit human error to gain access.
Attackers are using patched bugs to potentially gain unfettered access to an organization's Windows environment under certain conditions.
Winnti once used a variety of malware but is now focused on SQL vulnerabilities and obfuscation, updated encryption, and new evasion methods to gain access.
### Description Authentication using Spid and CIE is based on the SAML2 standard which provides for two entities: Identity Provider (IdP): the system that authenticates users and provides identity information ( SAML assertions ) to the Service Provider, essentially, it is responsible for managing user credentials and identity; Service Provider (SP): The system that provides a service to the user and relies on the Identity Provider to authenticate the user, receives SAML assertions from the IdP to grant access to resources. The library `cie-aspnetcorerefers` to the second entity, i.e. the SP, and implements the validation logic of the SAML assertions present within the SAML response . The following is a summary diagram of an authentication flow via SAML: 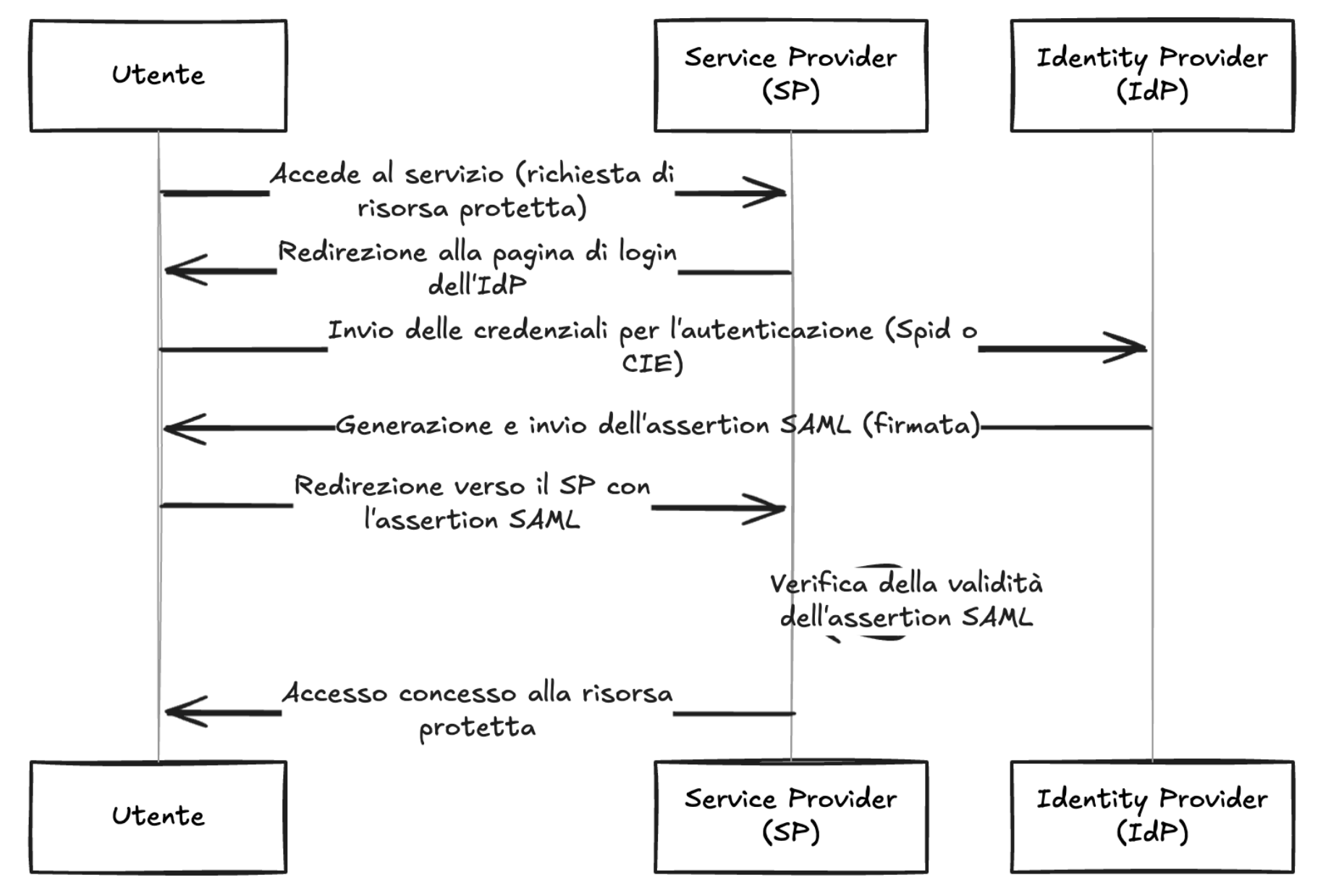 As shown in the diagram, the IdP, after verifying the user's credentials, generates a signed SAML response, this is propagated to the SP by the use...
### Description Authentication using Spid and CIE is based on the SAML2 standard which provides for two entities: Identity Provider (IdP): the system that authenticates users and provides identity information ( SAML assertions ) to the Service Provider, essentially, it is responsible for managing user credentials and identity; Service Provider (SP): The system that provides a service to the user and relies on the Identity Provider to authenticate the user, receives SAML assertions from the IdP to grant access to resources. The library `spid-aspnetcorerefers` to the second entity, i.e. the SP, and implements the validation logic of the SAML assertions present within the SAML response . The following is a summary diagram of an authentication flow via SAML: 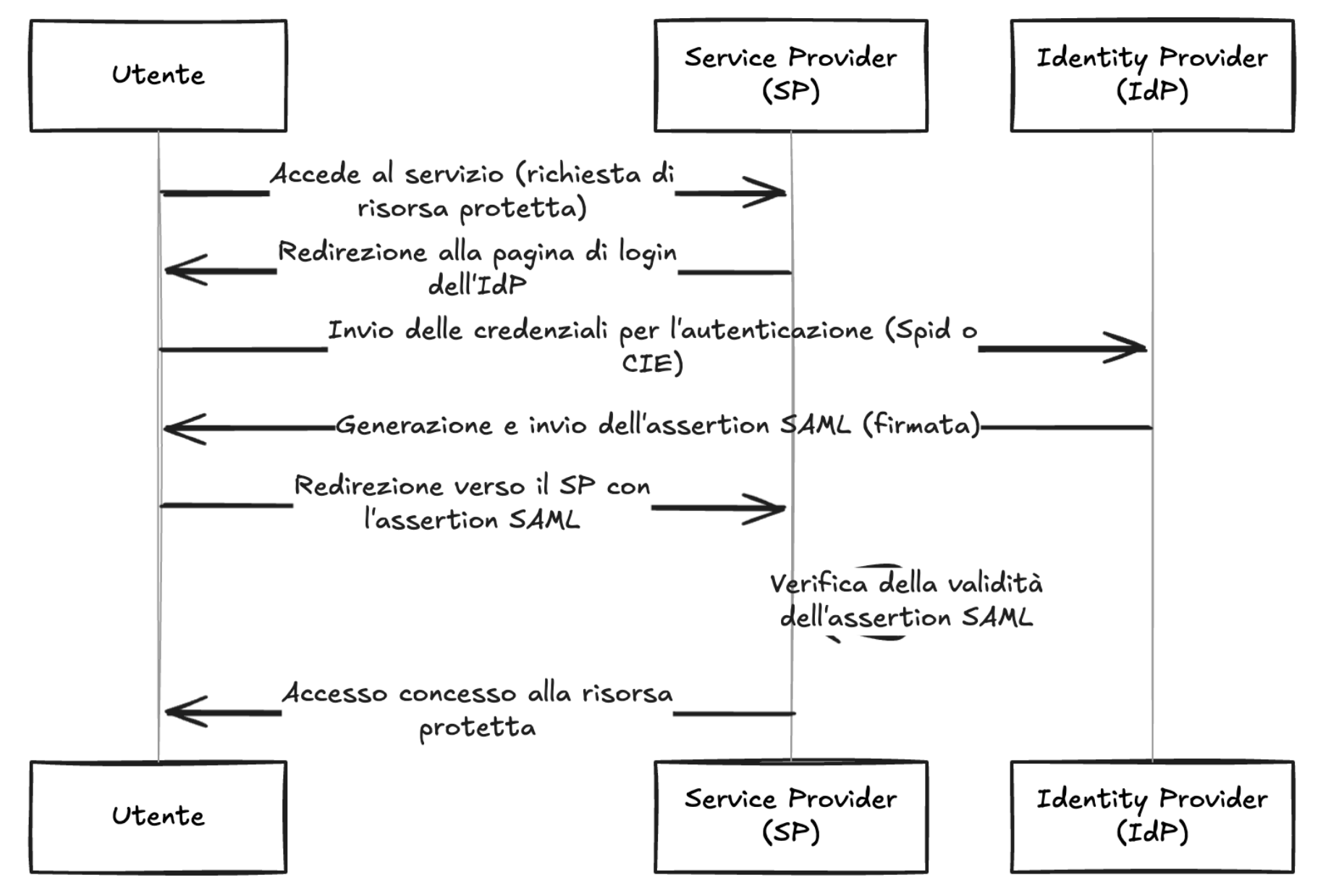 As shown in the diagram, the IdP, after verifying the user's credentials, generates a signed SAML response, this is propagated to the SP by the us...
Microsoft is warning the modular and potentially wormable Apple-focused infostealer boasts new capabilities for obfuscation, persistence, and infection, and could lead to a supply chain attack.