Tag
#java
### Summary There is improper sanitization on Service template name which is reflecting in delete button onclick event. This value can be modified and crafted as any other javascript code. ### Vulnerable Code https://github.com/librenms/librenms/blob/a61c11db7e8ef6a437ab55741658be2be7d14d34/app/Http/Controllers/ServiceTemplateController.php#L67C23-L67C23 Above is vulnerable code line which needs to be properly sanitized ### PoC 1. Go to /services/templates 2. Enter name as `testing', '14', 'http://172.105.62.194:8000/services/templates/14');alert(1);//` 3. Submit it and try to delete it, you will see popup If you inspect element on delete button, you will notice this:- <img width="748" alt="Screenshot 2023-11-23 at 9 30 24 PM" src="https://user-images.githubusercontent.com/31764504/285260018-7672a93d-e29b-4444-8057-e6ffcb8dabfc.png"> ### Impact Cross site scripting can lead to cookie stealing or an attacker can execute any other feature using this feature.
### Summary when jadx parses a resource file, there is an escape problem with the style file, which can overwrite other files in the directory when saving the decompile result. Although I don't think this vulnerability realizes path traversal in the true sense of the word , I reported it anyway ### Details I see that getResAlias does something with the filename. ```java private String getResAlias(int resRef, String origKeyName, @Nullable FieldNode constField) { ``` but type style will return the original filename directly. 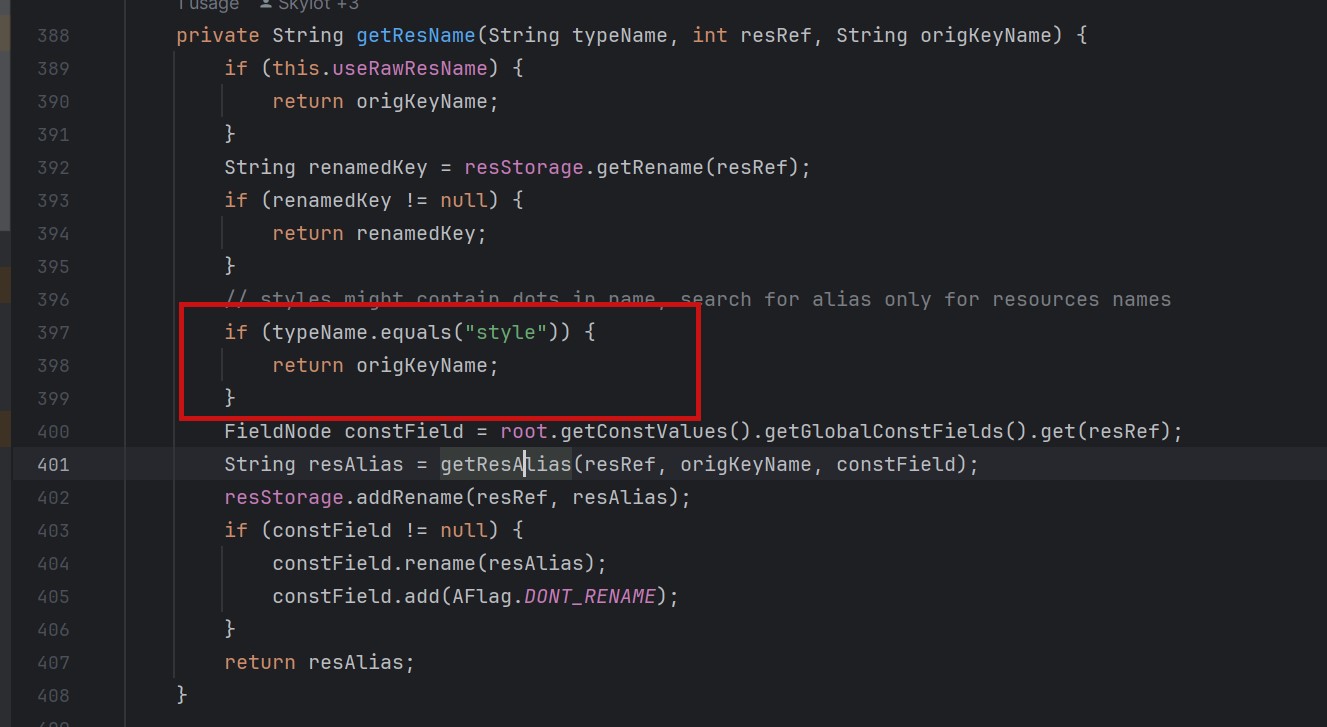 so our goal is to take a malicious file that was originally of type raw, modify its type to style, trick jadx into #### step1 create an android project using androidstudio and create a raw folder with the name attack_file_sayhiiiiiiiiiiiii, it doesn't matter what the content is! 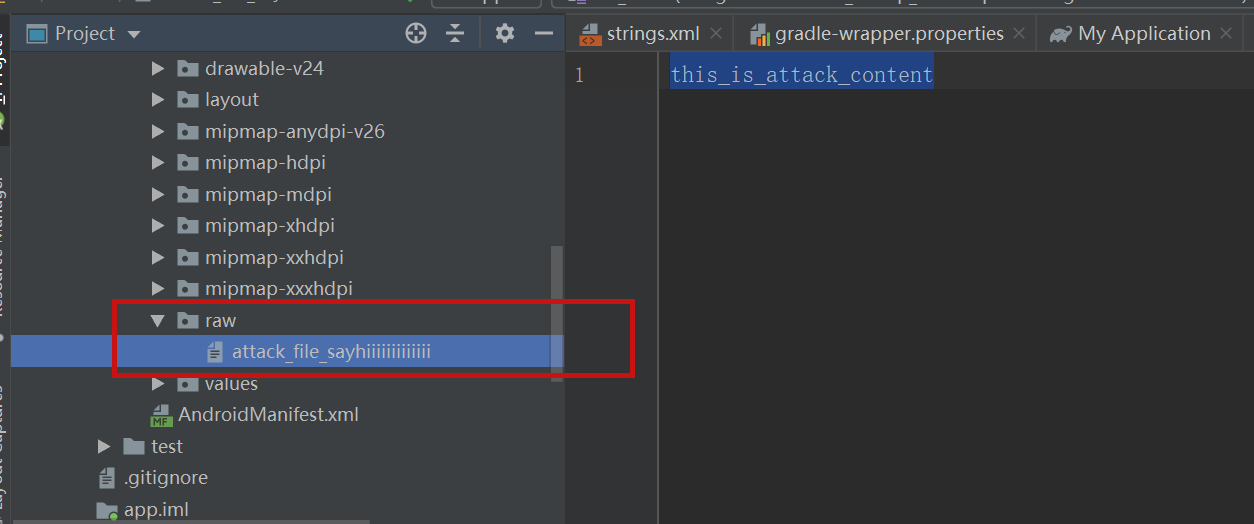 generate an initial APK #### s...
### Impact We have identified a local privilege escalation vulnerability in Ant Media Server which allows any unprivileged operating system user account to escalate privileges to the root user account on the system. This vulnerability arises from Ant Media Server running with Java Management Extensions (JMX) enabled and authentication disabled on localhost on port 5599/TCP. This vulnerability is nearly identical to the local privilege escalation vulnerability CVE-2023-26269 identified in Apache James. Any unprivileged operating system user can connect to the JMX service running on port 5599/TCP on localhost and leverage the MLet Bean within JMX to load a remote MBean from an attacker-controlled server. This allows an attacker to execute arbitrary code within the Java process run by Ant Media Server and execute code within the context of the “antmedia” service account on the system. ### Patches 2.9.0 ### Workarounds Remote the following parameters from antmedia.service file ```-Dcom....
Authentication Bypass by Spoofing vulnerability in Apache HugeGraph-Server.This issue affects Apache HugeGraph-Server: from 1.0.0 before 1.3.0. Users are recommended to upgrade to version 1.3.0, which fixes the issue.
Server-Side Request Forgery (SSRF) vulnerability in Apache HugeGraph-Hubble. This issue affects Apache HugeGraph-Hubble: from 1.0.0 before 1.3.0. Users are recommended to upgrade to version 1.3.0, which fixes the issue.
RCE-Remote Command Execution vulnerability in Apache HugeGraph-Server.This issue affects Apache HugeGraph-Server: from 1.0.0 before 1.3.0 in Java8 & Java11 Users are recommended to upgrade to version 1.3.0 with Java11 & enable the Auth system, which fixes the issue.
Debian Linux Security Advisory 5664-1 - Jetty 9 is a Java based web server and servlet engine. It was discovered that remote attackers may leave many HTTP/2 connections in ESTABLISHED state (not closed), TCP congested and idle. Eventually the server will stop accepting new connections from valid clients which can cause a denial of service.
Red Hat Security Advisory 2024-1880-03 - An update for the nodejs:18 module is now available for Red Hat Enterprise Linux 8.8 Extended Update Support. Issues addressed include denial of service and privilege escalation vulnerabilities.
### Summary A prototype pollution in derby can crash the application, if the application author has atypical HTML templates that feed user input into an object key. Attribute keys are almost always developer-controlled, not end-user-controlled, so this shouldn't be an issue in practice for most applications. ### Details ``` emit(context: Context, target: T) { const node = traverseAndCreate(context.controller, this.segments); node[this.lastSegment] = target; this.addListeners(target, node, this.lastSegment); } ``` The emit() function in src/templates/templates.ts is called without sanitizing the variable `this.lastSegment `. The variable `this.lastSegment ` can be set to `__proto__`, and this will pollute the prototype of Javascipt Object (`node['__proto__'] = target`). ### PoC To reproduce this vulnerability, you can adjust the test case `ignores DOM mutations in components\' create()` in `test/dom/ComponentHarness.mocha.js`. ``` it('ignores DOM mutations in components\' ...
### Summary A stored XSS vulnerability in Excalidraw's web embeddable component. This allows arbitrary JavaScript to be run in the context of the domain where the editor is hosted. ### Poc Inserting an embed with the below url (can be copy/pasted onto canvas to insert as embed) will log `42` to the console: ``` https://gist.github.com/vv=v<script>console.log(42)</script> ``` ### Details There were two vectors. One rendering untrusted string as iframe's `srcdoc` without properly sanitizing against HTML injection. Second by improperly sanitizing against attribute HTML injection. This in conjunction with allowing `allow-same-origin` sandbox flag (necessary for several embeds) resulted in the XSS. Former was fixed by no longer rendering unsafe `srcdoc` content verbatim, and instead strictly parsing the supplied content and constructing the `srcdoc` manually. The latter by sanitizing properly. The `allow-same-origin` flag is now also set only in cases that require it, following the...